Internet of Things (IoT) is gaining a lot of relevance in today’s world and is considered to be the next business revolution enabled by technology influencing everything and everyone. Most of us are getting impacted without even knowing about it, and yet we do not have enough nuances to understand this space in detail.
It is critical for us to deep dive and really understand how IoT brings about a transformation into our lives as well as how organizations across verticals are benefitting by implementing these solutions. Let us delve a bit more in detail and understand in a simple way the components of an IoT solution:
- Device side: All devices that transmit data acting as a data source
- Cloud side: That accepts data and provides ways and means to analyze it
Looks quite straightforward right, but it isn’t. Realistically it involves complex implementations involving multiple features and communication between the two sides through secure communication protocols. Ideally whenever we consider building an IoT solution, it should be cloud native (supporting public, private and hybrid clouds), microservices based, so it can be deployed independently, easy to troubleshoot, can scale as per expectations and even serverless, which means infrastructure and other resources can be provided on demand without a requirement to manage anything on premise.
ARCHITECTURE:
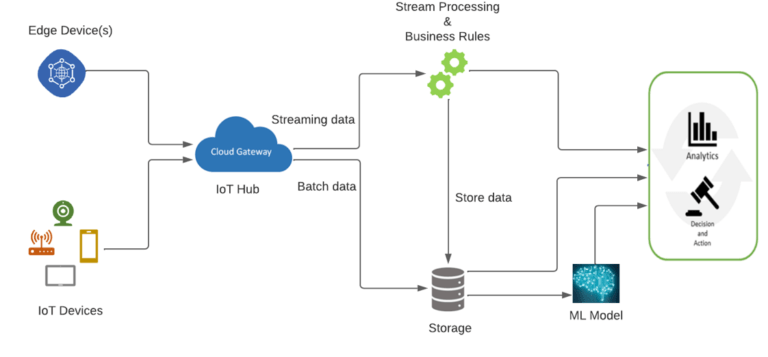
IoT and Edge Devices are the ones that can register with the cloud and has connectivity options for sending and receiving the data. Edge devices normally allow aggregation, transformation of telemetry data and on-premises processing before passing it on to the hub. The Cloud gateway or IoT hub accepts the data and provides device management capabilities. The data whether streaming or batch then gets processed with validation of business rules. Finally, it gets stored in a database and from there it can be analyzed by the user community in the form of dashboards / reports or fed into Machine Learning (ML) models to derive intelligence and take business actions.
SECURITY CONSIDERATIONS:
Having looked at the architecture of an IoT solution it is important to understand what it takes to secure the solution. Security is therefore a critical consideration for each of the subsystems specified below:
- Device Security – software / firmware & physical device security, to ensure the device can’t be hacked.
- Connection Security – Network security to ensure that the connection between the service provider and your phone is secure as there are many devices transmitting data. Another aspect is making sure “data in motion” is as secure as “data at rest”, meaning the data that gets stored in a database on the cloud is not exposed to hackers.
- Secure Cloud Services – Ensuring Cloud services you use is secure and protects your network while storage options are secure too and protect your data.

Some measures that can be taken to improve the security of the physical device are:
- Choosing microcontrollers / microprocessors or auxiliary hardware that provide secure storage
- Using sensors to detect intrusion attempts and attempts to manipulate the device environment through alerts
- By providing a unique identity key for each device, which can be used by the IoT infrastructure to communicate with the device while it is in operation
On the other hand, the firmware and application software on the device must allow for updates to enable the repair of discovered security vulnerabilities.
Connection security should ensure that the communication path between devices and IoT Hub or between edge devices and IoT Hub are secured using industry-standard Transport Layer Security (TLS).
Today’s cloud service providers such as Azure, AWS, GCP etc. ensure that the services are built with security in mind, but architects still need to evaluate how data flows through any service. Data is the responsibility of the data owner and not of the service provider.
It is important to also understand the best practices to be adopted from a security perspective, following are some of them:
- Competent Team: The team needs to be strong and competent. Whether it includes your Hardware Manufacturer, from where you buy devices, understanding their support model and whether they update their firmware regularly to the people who develop the code, deploy it and use the devices.
- Device Security: We talked about the same earlier, ensuring the updates / patches are properly applied to, the device is tamper-proof to ensure that the data & keys can be erased from it during disposal.
- Network Security: Extremely critical when transferring data to other devices, ensuring authentication and encryption are taken care off
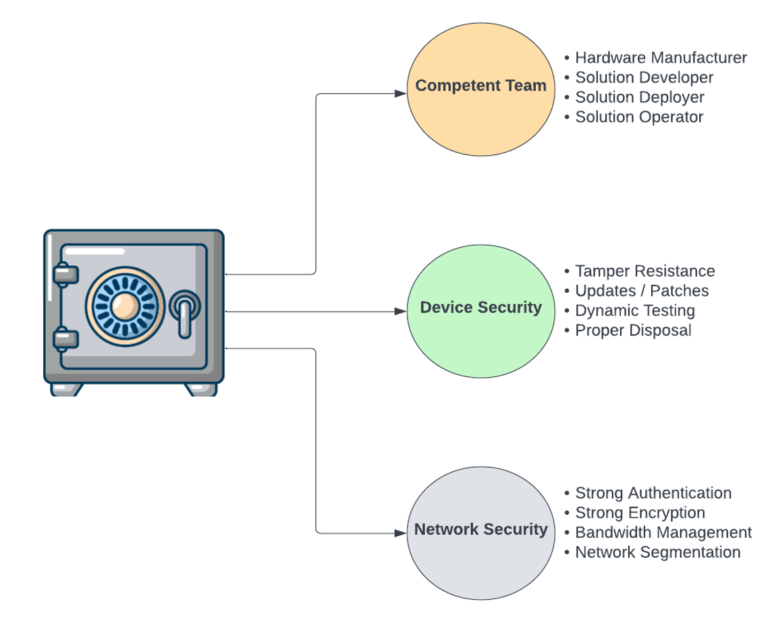
IoT Architects should design a security plan that fits the needs of their solution. Security should be a primary consideration when developing an IoT architecture. Security is always the responsibility of the engineers that build the system, making it an integral part of the design from day one as it helps to mitigate problems later in development and deployment.
INDUSTRY VERTICALS & USE CASES:
After having talked about what exactly is IoT, Architecture and Security considerations, let’s now understand what role IoT plays in a some of Industry Verticals that we have worked with and how the solutions offered did benefit the organization substantially improving its operational efficiency.
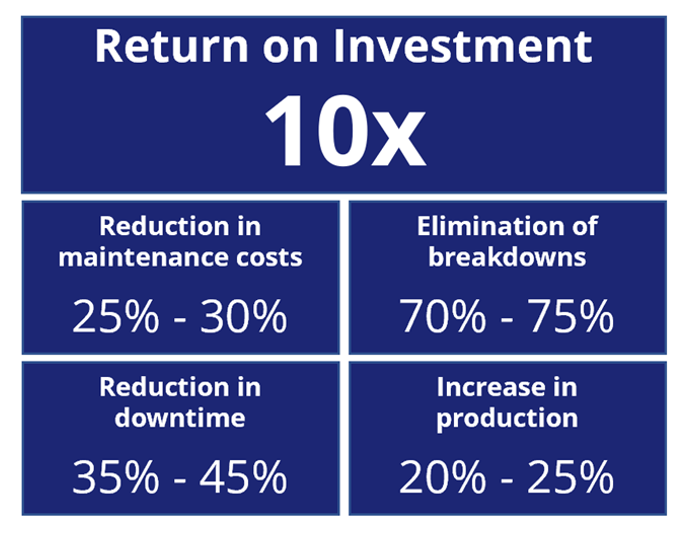
IoT in Manufacturing and Use Case on Predictive Maintenance (PM):
IoT is transforming the Manufacturing Industry in general and we have seen obvious benefits associated with organizations who are implementing it. Let’s take an example of a Predictive Maintenance (PM) use case.
Some tangible benefits of Industrial Analytics for Predictive Maintenance are as follows:
Predictive Maintenance Process:
- Data is collected over time to monitor the state of the machine
- Analyze the data to find patterns that can help predict & ultimately prevent failures
Address the following concerns:
- Remaining Useful Life (RUL) Prediction – when a machine is likely to fail, so as to schedule the maintenance in advance
- Anomaly detection – Irregular behavior of machines
- Failure Diagnosis – Recommendation of mitigation steps
Data collected through sensors placed on the machines is sent to the IoT gateway from there it is sent to the Cloud at regular intervals of time and fed into a Machine Learning (ML) model to find patterns, that address the above concerns.
Data Collection from Machines, that help in predictive maintenance is detailed below:
- Static data: Equipment related data e.g., Make, Model etc.
- Frequently updated data: Usage History e.g., Age in Days / Hours etc.
- Occasionally updated data: Maintenance data e.g., parts replaced, date of replacement, service history etc.
- Time-series data: IoT Signal e.g., Heat, noise, vibration, voltage etc.
- Other data: Data from systems, manufacturing process, past breakdowns etc.
Building ML Prediction Models:
- Regression Model for determining Remaining Useful Life (RUL)
- Classification Model for determining Failure
The model building and validation will follow a series of steps outlined below:

Benefits of PM Models:
- Reduces Downtime
- Increases Productivity & Operational Effectiveness
- Understands root causes of failures
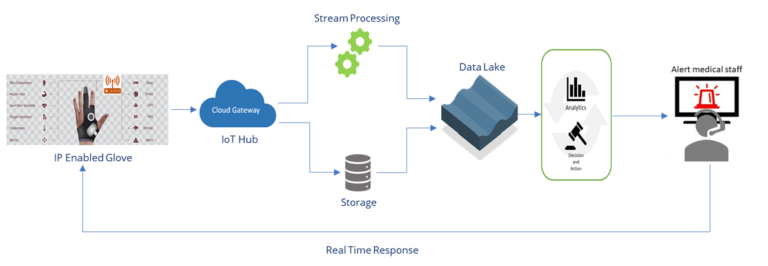
IoT in Healthcare and associated Use Case:
Another interesting use case for which we successfully completed a pilot was in the Healthcare arena.
A Healthcare startup developed a smart glove capable of sensing electrical signals from the body, keeping track of the health and letting the patient know, how they are doing while they sleep, work and go about their daily routine.
This product was designed for the early detection and management of epilepsy that helps to make the lives of people with epilepsy safer and remove some of the uncertainties, they deal with every day. The organization was also trying to make it easier for doctors to arrive at a more accurate and faster diagnosis, with the help of streaming real-time data, collected over different periods of time.
The glove had several sensors that can extract information from the palm of a hand and transmit this continuously to a personal data gateway and intelligent system that comes with the glove. This information is then sent to the Cloud environment at set intervals.
We extracted this from the Cloud storage and brought it into a Big Data Platform and analyzed it to provide various Analytics that could help the doctors determine and monitor their patient’s health and provide real time response.
These case studies just scratch the surface of what can be done in this vertical. This space, perhaps more than any other vertical has the potential to positively impact billions of lives as it is nascent and emerging. Consider the numerous benefits IoT provides from hospitals to home e.g., easing the process of admittance to keeping doctors (and patients) better informed to advancing in homecare as we have seen in the use case above to predicting the problems before they occur and many more..
To conclude IoT is impacting everyone in different ways. It is important for all of us to understand the impact, relevance and considerations while implementing these solutions. Businesses have begun to adopt the technology and the demand for these solutions will be growing exponentially over the next decade. No doubt, it will prove to be the next big wave in technological advancement!
Parag Penker
GLOBAL VICE PRESIDENT – TECHNOLOGY (BIG DATA, DATA WAREHOUSING & BUSINESS INTELLIGENCE)
Parag is heading the Big Data, Data Warehousing and BI initiatives across the USA, India, Middle East and Africa. Parag carries more than 25 years of experience in the IT Industry and has PMP, Oracle Hyperion and SAP Supply Chain Certifications to his credit.
